

CISSP Database Keys Explained: Primary, Foreign, and Candidate Keys
Ugh, not this domain again! Haha, sorry I just can’t stand Domain 8 sometimes. I’m more of a firewall engineer, and not so much a dev guy. But, you gotta know if you wanna become a CISSP! Relational databases rely on structured relationships between tables. These relationships are controlled through database keys . Just know the definition of the three types of keys below, taking note that the PRIMARY one is the most important. For CISSP candidates, understanding keys is
Mar 17

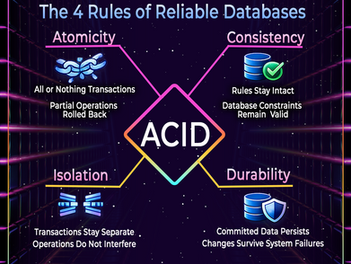
ACID Principles Explained for CISSP: Databases Must Be Reliable
ACID! Just a cool word to begin with, and the CISSP definition of it is even cooler. Whenever I start studying anything in the Domain 8 pages of CISSP books, I just can’t wait to get to the easy topics, one of which is ACID. It just focuses on the reliability of database transactions. ACID represents the core design principles that ensure databases process transactions safely and predictably. ACID stands for: Atomicity The word atomic comes from the idea of an atom in physic
Mar 17


CISSP Database Architecture Basics: Tables, Relations, Cardinality, and Views
Not exactly my favorite topic, or any topic in Domain 8! But you just don't know what the CISSP exam will test you on, so best to just know all of it at a surface level. Believe me, I have zero experience with software development, so Domain 8 was particularly difficult for me while studying for the exam. Not so much now that I'm an instructor :) Just know the basics below, nothing crazy: Relational databases organize information using a structured model built on tables an
Mar 17


Gotta Know Data Lifecycle for CISSP
Data Handling Requirements: Marking, Labeling, Storage, and Destruction Domain: Asset Security / Security and Risk Management Data handling spans the entire data lifecycle : how information is labeled, stored, accessed, and ultimately destroyed. The risk doesn’t disappear when data is no longer useful. In many cases, that’s when risk quietly increases. Residual data, unintended retention, and improper destruction methods are classic examples of controls that look sufficient
Feb 19


How Rohan Cracked His CISSP Exam
Hello All, Kindly find the approach I followed for the CISSP certification. I started the CISSP journey initially in March 2022, with an online training course conducted by Mr. Saaz Rai. This course helped to gain valuable insights about the CISSP certification and concepts and the exam outline. I could only start the studies seriously from October 2022 onwards (after a period of 7 months). I started getting up early at 4 AM for studies and planned my day accordingly. Some
Feb 19
